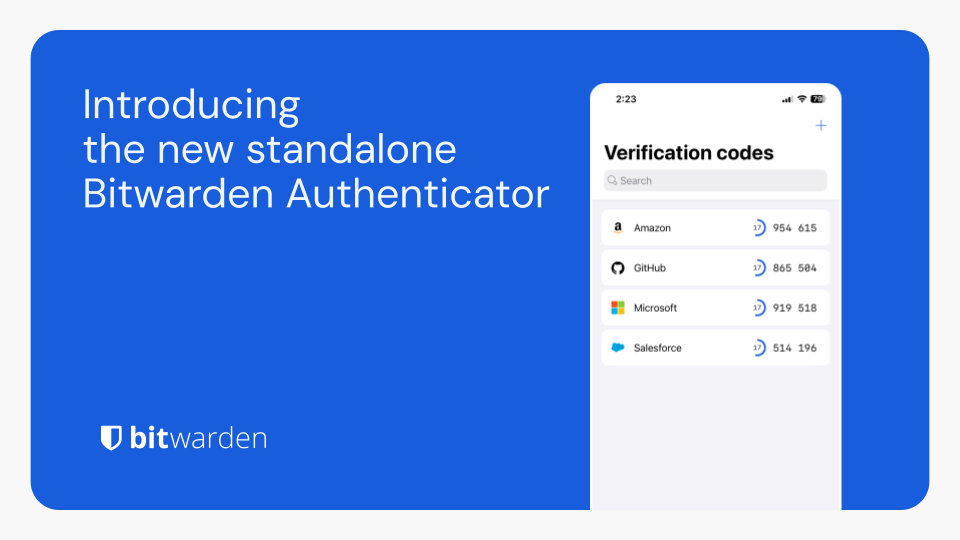
Bitwarden Authenticator is a standalone app that is available for everyone, even non-Bitwarden customers.
In its current release, Bitwarden Authenticator generates time-based one-time passwords (TOTP) for users who want to add an extra layer of 2FA security to their logins.
There is a comprehensive roadmap planned with additional functionality.
Available for iOS and Android
To those that are confused about this:
Bitwarden does indeed handle TOTP directly in the password manager, but only on paid accounts and only logged in.
This is a completely offline app, separate from your existing Bitwarden account, that is entirely free.
It might serve as an alternative to e.g Aegis to some.
Is there a good reason I don’t know about to prefer this over Aegis?
No, they’re both ostensibly open source and standalone. I’m an avid Bitwarden Free user, but Aegis has been my go-to for a long time.
If it’s a standalone completely offline app, like Aegis, I’m at a loss to what they could offer that is any different than what Aegis already offers.
If you look at the roadmap they have in the blogpost, they are apparently planning tighter integration with the existing bitwarden suite
…but wouldn’t that undermine the fact that it’s standalone and offline?
The idea is that it can then work both says, like https://ente.io/auth does
Sand the fact that it’s a 2fa. A thicker integration with bitwarden would make it like a 1.5fa
I don’t see why it would if it’s optional
How so? They already have TOTP built-in to the app if you pay for premium, so this is just a free competitor to their own offering.
I’m guessing they’re trying to make it a “gateway” to getting people on Bitwarden. Start with the TOTP app, then use the password manager, then pay for premium. Or something like that.
2FA push is on the roadmap. Does aegis have that? Or am I just too dense to realise it does?
I mean, Aegis is 2FA? That’s literally all it is? It generates One Time Pad codes for various sites and apps that support authentication apps.
So, I’m not sure what you mean?
I’m not positive but I’m assuming they’re referring to a kind of MFA where the authenticating service pushes to the client you possess rather than relying on a temporal cryptographic key. I’ve got a few services which work that way
That’s indeed what I meant. Similar to how OKTA, battle.net, or the Microsoft authenticator works( in corporate environments).
You receive a push notification which asks if you’re trying to log in and approve it, followed by a fingerprint or a pin code to confirm, rather than having to type in the code generated by your app
Reading these comments, it feels like Aegis became the standard without me noticing.
Reading these comments I feel like I’m completely out of the loop because I’ve never even heard of Aegis
It doesn’t get a whole lot of attention but it’s the most mature open source authenticator app and one of the first ones you would find in fdroid. With that said, there’s nothing really standout about it or its features, it just works.
same
Just on Lemmy
interesting. what makes it special? i’m assuming it’s just like any other TOTP client?
Someone answered this for me. It’s just that it’s open source. If that matters to you, there you go.
I used to use Aegis, but after setting up my own vaultwarden, I use the normal bitwarden app/plugin on all my systems for passwords and TOTP.
The advantages are that I don’t need my phone to login, the keys are synced and backuped in the encrypted vaultwarden database, which I can then handle with normal server backup tools. It still works offline, because bitwarden app caches the password.
This is IMO much more convenient and secure (in a way that loosing access to a device doesn’t shut you out, and you don’t need to trust third parties) then most other solutions.
Even if I hosted my own BitWarden vault, I wouldn’t put my passwords and 2 factor tokens in the same place because it’s eliminating the benefits that 2 factor provides if someone somehow manages to get into my vault.
2 factor came into our life because people were using same passwords everywhere. With unique passwords, which are easy with password managers, it’s rarely needed.
That may have been part of the reason, but the theory behind MFA is that there are 3 primary ways to authenticate who you are: what you know (password), what you have (secure one time password generator or hardware token), and what you are (biometrics). Password managers and digital one time password generators have kind of blurred the lines between passwords and one time passwords, but you’re raising your risk a bit if you put them in the same place.
With unique passwords, the attack surface just changes. Instead of attacking the passwords, attackers attack the password managers. LastPass, Okta, and Passwordstate each had breaches, and the first two are quite popular.
That doesn’t mean Bitwarden is at risk (not sure if it has been targeted), it just means that attackers are finding success going after password managers, so they could go after Bitwarden. Maybe they’ll sneak in an xz-style bug that’ll allow attackers to steal credentials en-route, idk.
So it’s a matter of good/better/best:
- good - use a password manager to prevent password leaks from providing access to other accounts
- better - use 2FA to prevent “password recovery” attacks; these are often targeted in nature, so there’s a lot less risk here
- best - use a separate 2FA from your password manager to prevent a breach from exposing all of your accounts
The overhead from using a separate 2FA app is pretty low, just make sure it encrypts your keys and you trust it (FOSS is a good indicator of trust).
There is not much difference between having two apps (password manager and authenticator app) or one app, that does both on the same device.
So, if you want more security, then you have to deal with a hardware token and never with a authenticator app. But then if you loose your token, then you have trouble.
I don’t think it caches the password. Rather a decryption key is derived from your password and is used to unlock the encrypted blob.
What I meant is that is caches the password database for offline use.
For now: No.
At this moment Aegis is far superior to bitwarden auth. But it looks promising.
I really like the ability to “sideload” the icons for the codes and automatic encrypted backups to cloud storages.Not switchin’ from Aegis. No sir’ee.
I use the TOPT features and i dont have a paid account
Do you self-host? I think that’s another way to get the TOTP features w/o a paid account.
Probably but i am not
It might serve as an alternative to e.g Aegis to some.
Does it have any killer features in favor of using the free app of an for-profit company instead of an established FOSS app?
Bitwarden apps have been open source since the beginning, mobile + backend + web
I haven’t been entirely happy with Bitwarden for other reasons. You can’t self host and share with one other person without paying them $40/year. Their advertising is deceptive, because they say you can do both for free. But that one or the other, not both.
You also can’t easily share individual passkeys outside of the app. If you want to grab a passkey, you have to export your entire vault.*
It’s basically annoyance-ware.
* note that sharing passkeys is not best practice, but there are use cases.
I don’t think I realized that was a limitation because I’ve been using the Vaultwarden fork. https://github.com/dani-garcia/vaultwarden
Have you heard if VaultWarden?
As others have said vaultwarden is the solution here. It is free, you can manage multiple vaults, totp is free. All the platform bit warden apps & plugins work with it. Supposedly it is leaner and easier to set up. Don’t know for sure because it is all I have used.
For shared passwords, I have a family vault where I put my streaming pws and such and everyone has access without having to share my personal vault.
Yeah, VaultWarden sounds like the answer.
with full Internet access (As shown in Aurora Store)
Thanks but I pass, I’d rather use Aegis that doesn’t need internet connection at all.
How does 2FA work without an internet connection?
it’s basically just a shared random number generator on a timer (it’s slightly smarter than that but that’s the gist), so as long as you know the start time, the current time and the starting point for the RNG, both parties can get the same result without having to ever communicate
deleted by creator
Thank goodness! I can finally get the hell away from Authy!
What’s wrong with Authy?
Not open source, and I believe an account is required.
Also doesn’t allow you to export so you can’t switch to another service
Also they have weird behind the scenes integrations into accounts even if they are just supposed to be regular 2FA. You can read stories about Twitch not playing well with other 2FA until 30 days after you remove Authy. I don’t want those kind of shadow integrations and I should be allowed to switch apps as I see fit
Uhg… Didn’t know that part. So frustrating.
And twilio, the parent company has been hacked before
I guess for me, it being closed-source and the fact that the Bitwarden password manager and now Bitwarden authenticator are open source. Truthfully, I just see how they handled the desktop version of their Authy software, giving no fucks if consumers wanted it or not, being a big red flag of what could come after. Having used Bitwarden for years now, and giving them $10 a year, makes me more biased and inclined to use their other software, since they’ve never let me down. :)
I use Aegis and it works well. FOSS and easy to use.
They discontinued the desktop client about a month ago, which is what made me stop using it.
Too many things use it, if it becomes compromised that is way too broad of an attack for me to opt into
You could have before. I moved from Authy to Aegis a few months ago
Correct me if I am wrong, but the Bitwarden client itself already does this. I store several of my TOTP’s in my self hosted Vaultwarden/Bitwarden install.
And where would you store your Bitwarden login TOTP if you used their service instead of self hosting?
And what happens if your Bitwarden account gets compromised? Now you’ve lost both factors at the same time.
No, I’ll keep my 2FA separate from my password manager, thank you very much.
Good luck getting your vault compromised.
Unless you have a weak password or the vault isn’t encrypted (which it is, AES256 iirc and you might be able to change that on a self hosted version), I don’t see that happening.
Most password manager hacks don’t attack the encryption or password themselves (my password is very long), they find/create a side channel. For example:
- keylogger attack to grab password manager password
- social engineering to reset a password
- attack the server to intercept passwords
Every secure system can be defeated, but it’s a lot less likely that two secure systems will be defeated at the same time. So I keep my passwords and second factors separate. It’s unlikely that either will be compromised, and incredibly unlikely that both will be compromised at the same time.
You’re right, it does. This is a head-scratcher.
I guess they already had the TOTP code written, so creating a standalone app was trivial, but what’s the point?
Security-wise it’s not a good idea to keep passwords and 2FA codes in the same client as it then becomes a single point of failure. A standalone authenticator app resolves that as long as it’s not unlocked with the same master password. A standalone app also opens a venue for non-BW customers to get on their platform.
Would it count if the application is the same but all the TOTP is handled by a different database with a different passphrase?
Depends on how they got broken
It’s not a good idea to keep both on the same device, but i wouldn’t use it at all if it was a struggle
TOTP in the Bitwarden Vault is a paid feature. The standalone app is free, and doesn’t even require a Bitwarden account.
This allows free tier users a way to use TOTP without upgrading, and without needing to trust Google Authenticator or something else.
TOTP code is like 5 lines. The hardest part is writing the seed to disk.
thd totp in the default application is paid and that isn’t
Because you can enable totp on your Bitwarden account and it would be dumb to store the password and totp for your biwarden vault in your vault?
Also it can act as a stepping stone for non Bitwarden customers, before getting their own vault.
Glad these were answered:
Isn’t this the same as storing TOTP authentication codes in Bitwarden Password Manager?
Integrated TOTP authentication is a premium feature in Bitwarden Password Manager. Bitwarden Authenticator is a standalone mobile app that generates TOTP codes for any online service that supports them. Bitwarden Authenticator can be used without a Bitwarden account.
Should I use both? When should I use the integrated authentication feature? When should I use Bitwarden Authenticator?
Integrated authentication in Bitwarden Password Manager offers a convenient way for users to add 2FA to their online accounts. This popular feature will remain available across paid plans.
Bitwarden Authenticator can be used to store your verification codes to access your Bitwarden account, as well as other online applications you use.
They can be used together, or separately, depending on your security preferences.
Great. Now I have to make the effort of migrating from Authy.
Does this save to my cloud account with them or is it only local? I got screwed over by Aegis (my fault) when I got a new phone and forgot to back up Aegis and lost a lot of my logins. Some of them I can’t get unless I call the company and verify it’s me 🤦🏽♂️
Do backups kids. :)
I actually keep an authenticator app on my desktop, so I always have two places for everything. Aegis on my phone and “Authenticator” on my Linux desktop.
Wait, I’m a second child, am I a backup kid?
Then how do you secure the backup without 2FA?
Or is it 2FA all the way down?
You could store it on an external drive. You can encrypt it with VeraCrypt as well.
Aegis encrypts it with a password, then you copy it somewhere. It’s just a set of keys and you can have as many copies as you want (I have three, one phone and two desktops).
Aegis doesn’t run on your desktop using the same key, it’s just a key stored there, right?
No, I use a different authenticator app (called Authenticator in the Flatpak store), but it does use the same keys. So I import the keys from an Aegis dump so I can generate exactly the same keys on my desktop app that I do on my phone.
TOTP is a really simple system, as long as I have access to the secret key and a reliable time source, I can generate the exact same tokens as any TOTP app would.
I backup everything, but Aegis
How do I do the backup for Aegis? I looked at it and it’s set up but then at the bottom it says no backups have been made 🤔
Settings > Import/Export > Export
This dumps it to a file, then it’s on you to copy it somewhere else.
Or
Settings > Backups
I think this one is automated, but I personally don’t use it, I just back it up manually when I add something new. I keep a completely functional 2FA app on my desktop, so I always have a backup in a pinch.
Thanks!
Aegis does automatic backups. I guess you didn’t turn it on?
Guess I didn’t. I hate me even more now
The penguin is dead 😂
😂 I guess it is. Damit
I spelled your username wrong. I thought the q was a g. 😂
I don’t care. It’s meant to be a penguin with a q.
Yubikey and yubico authenticator is king. Just need multiple keys. Stick it in a PC or tap it on your phones nfc… bam totp code pulls up.
After Authy scrapped its support for the desktop client, I’m looking for an alternative. Sadly, this does not look like it.
Sadly, this does not look like it.
Why?
I do not see a desktop client.
Ah. I only use a phone app, but I see the problem.
Ente.io is working on a desktop app. Whilst its experimental, you can get it from the releases page on their github
I use Authenticator on Linux. I’m not sure what OS you use, but perhaps there’s another, TOTP is a pretty easy protocol to implement (it’s basically just a hash of a key and timestamp).
I would like an app for desktop and phone/tablet that are syncing, just like Authy did, before they abandoned the desktop app.
So, for me that means: iOS/iPadOS and macOS
I’m in the same boat. I’m a paid Bitwarden user but I’d like to keep 2fa and passwords separated.
If no alternative soon, i’ll just bite the bullet and put everything in bitwarden (except itself, ofc)
Just like in the password manager, they ignored HOTP. Oh well.
Could you tell me more ?
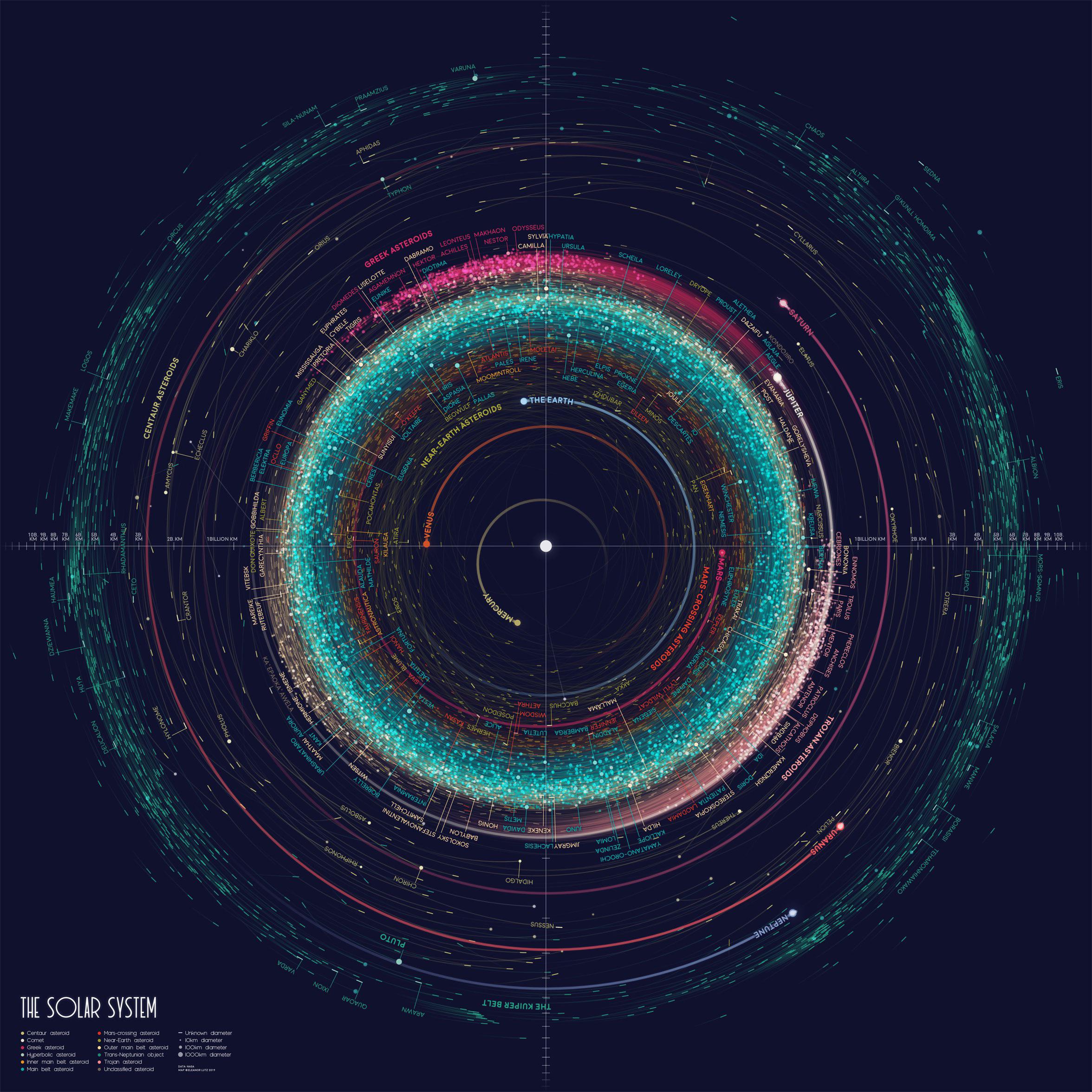
HOTP is an HMAC-based OTP, whereas TOTP is a time-based OTP. Basically, this is how each works:
- HOTP - based on a key + a counter, which increments with each code generated
- TOTP - based on a key + time, so you get a new key every N seconds
TOTP is quite common and honestly is all I use, whereas HOTP may be more common in certain enterprises. Main criticisms:
- HOTP - longer time window for a key to be valid for the entire time between logins (i.e. potentially easier to brute force)
- TOTP - less user-friendly due to the time window; also, you just need a clock, you don’t need to know the counter value (if someone gets the key, they can generate keys whenever)
Gotcha, thank you very much.
OK, so one TOTP app more. What’s this one doing better than all the others like 2FAS?
one TOTP app more
You say this as a bad thing.
Not at all, I’m just wondering if this particular one is better than any of the others.
Yeah, they’re are a few open source TOTP apps that seem pretty interchangeable. I use Authenticator Pro because it has a Wear OS integration that is handy if you have a smart watch.
For now: Nothing. Pretty bare metal atm.
deleted by creator
Nice! I currently have a couple of services on MS Authenticator that I can migrate over.
What makes you switch to this one rather than staying on MS?
Edit: oh no I asked a question that is obvious to others
MS not trustworthy
Honestly? This.
The less I have to rely on Microsoft or googie for anything, the better.
Microsoft’s Authenticator app is AWFUL. Just one example - there is a setting to backup to iCloud, but when you try to enable it, it demands you add a secondary (personal) Microsoft account.
I didn’t know it sucked on the iPhone, I haven’t had problems on Android, I actually quite like it. I would only change to get away from Microsoft
KeePassXC can do this as well. I had no idea until I saw a post on here where someone mentioned it. Here’s the documentation.
Jesus fuck. How many more authentication apps do we need that all do the same thing?
At work I need at least 4-5 different authentication apps because every customer has something different.
We don’t need another.
You only need one app, as long as the totp is implemented in a standardized way.
Microsoft products would like a chat…
I use my Microsoft account with a standard OTP app, you don’t need their own app.
Wait until your workplace requires you to only use MS Authenticator push notifications 😭 and HOTP occasionally…
Is that a thing? Usually those have a fallback to a regular TOTP code.
I use Okta for work because we integrate SSO with it everywhere, but I could technically enter a code every time and swap out the Okta app for the other TOTP app I use.
My company is a MS shop, but they use TOTP as the second factor, and even that is optional. My department uses Okta, which is a completely separate system (we’re a weird, separate unit entirely from most of the rest of the company).
I did too until it kept rejecting my tokens frequently - changing to M$ Authenticator “solved” it.
They must now require HOTP or something now. TOTP doesn’t care what machine it’s on, whereas HOTP does (well, you could spoof it if you really wanted).
They’re probably using HOTP or something else, not TOTP. TOTP is literally just the key + any clock. Or maybe it’s the “click button to authenticate” and not the “enter code to authenticate,” which might not be HOTP or TOTP, but something else entirely (e.g. Steam’s system is neither AFAIK).
If it’s TOTP, you just need to get the key and can use any authenticator app.
They did. DUO was born.
deleted by creator
4-5 TOTP apps? So far, when, e.g. Microsoft or Google have insisted use of their own Authenticator app is required, it’s worked fine for me using Ente Auth or similar just by entering the code / QR.
Yup, most 2FA is just TOTP, which is a pretty simple, open standard and is hardware independent. All you need is a key (the QR code or the numbers) and access to a reliable time source and you can make a TOTP app on anything.
I use Aegis on my phone and Authenticator on Linux (some GTK app), and they both produce identical codes for the same key.
This even works with some apps that hide the standard part - like Symantec VIP - it’s possible to extract what they are doing and use a standard TOTP app instead of VIP.
Random number generator 2fa?
I’m not putting my totp with my password, same as I’m not putting my password with my email (proton)
It’s a separate app with no sync to Bitwarden accounts.
Still, I bet they share a lot of the same backend and personell.
personell doesmt matter as it’s zero knowledge?
And seemingly reading beyond the headline is also not your thing.
This is a separate app unconnected to your bitwarden account…Exactly, from a security perspective, it’s a bad idea to put 2 factor tokens together with your passwords. You effectively eliminate the security benefit that 2 factor provides if you do because if people get into your password manager, they have everything they need to access your accounts. The only people it “helps” having it all in one app are people who don’t understand the purpose of 2 factor and just see it as an inconvenience when services force it on them. Even though I use BitWarden for passwords, I don’t think that I’ll be changing from Aegis to BitWarden’s stand-alone authenticator because Aegis is doing its job nicely.
That’s also part of why I’m against the new passkeys. I think passkeys could replace either passwords or tokens, but not both.
It really depends on your threat model. It’s not a one size fits all thing.
For instance in some threat models you shouldn’t have TOTP auth and passwords on the same device, let alone the same app, but the vast majority of people are not going to carry two devices because of how inconvenient it is.
Good. They make great stuff.